Special Bulletin Review: Securing our Citizens while Modernizing
-
Preventing breaches through cyber awareness: How every federal employee contributes to cybersecurity
Instead of waiting for cyber-specific positions to be filled, the White House has prioritized strengthening the current federal workforce through cyber education and skills-based training.
June 19, 2023 -
In March, the White House unveiled a new National Cybersecurity Strategy, which deviates from the National Cyber Strategy rolled out by the Trump administration in 2018. Among the changes implemented in the new strategy is a call to “rebalance the responsibility” of defending cyberspace, including a move away from end users and toward the “most capable and best-positioned actors,” including owners and operators of key technologies and infrastructures.
June 16, 2023 -
Air Force plans to recruit and retain cyber professionals include a new tech track career path set to debut next year.
June 16, 2023 -
Martin Rieger, the chief solutions officer and chief information security officer a stackArmor, said the caring, feeding, maintenance and continuous development of federal cyber regulatory and policy requirements is necessary for success.
June 16, 2023 U.S. officials say the Department of Energy is among a small number of federal agencies compromised in a Russian cyber-extortion gang’s global hack of a file-transfer program popular with corporations and governments. They say the impact is not expected to be great. Jen Easterly, director of the Cybersecurity and Infrastructure Security Agency, told reporters that the hacking campaign was short, opportunistic and caught quickly. A senior CISA official said neither the U.S. military nor intelligence community was affected. Known victims to date include Louisiana’s Office of Motor Vehicles and Oregon's Department of Transportation.
June 16, 2023-
Sources confirmed the Energy Department is treating it as "major incident," with other agencies uncovering intrusions as well.
June 15, 2023 -
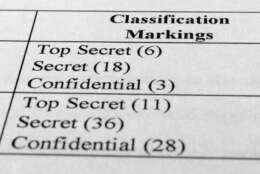
How do you stop a 21-year-old national guardsman like Jack Teixeira from leaking classified information? Wrong answers to this question have quickly become very popular.
June 15, 2023 -
Kurt DelBene, the assistant secretary for information and technology and chief information officer at the Veterans Affairs Department, said the agency is working on several parallel goals including getting to 100% use of multi-factor authentication.
June 15, 2023 -
A new instructional letter from the General Services Administration provides guidance for responsible use of generative AI by employees and contractors with access to GSA systems.
June 14, 2023 -
Amid the recent spate of high-profile cyberattacks, government agencies and private-sector organizations alike are scrambling to fend off unauthorized intrusions that can compromise digital assets, disrupt operations and derail attainment of critical missions.
June 14, 2023 -
The directive comes after suspected China state-backed hackers allegedly used network administration tools to access critical infrastructure systems.
June 13, 2023 -
The U.S. federal government possesses some of the strongest cybersecurity in the world with a GCI score of 100. This intense cybersecurity is no surprise, as the federal government is tasked with protecting the nation’s most precious assets, like classified data and critical financial information and defending against the most malicious, well-funded and motivated attackers. This large scope of the critical assets to defend has made the federal government one of the biggest spenders on cybersecurity in the world, and as cyber threats continue to evolve, investment in cybersecurity will continue to grow.
June 13, 2023 -
Because cyber threats ceaselessly change, so do the protective measures agencies need to take. Cybersecurity guidelines from the National Institute of Standards and Technology (NIST) never stay static either.
June 12, 2023 -
Dan VanBelleghem, a senior director, cybersecurity programs, at General Dynamics Information Technology (GDIT), explains how agencies can stay ahead of cyber attackers.
June 12, 2023 -
A memo released today extends the deadline for when agencies have to start collecting secure software attestation forms from vendors.
June 09, 2023