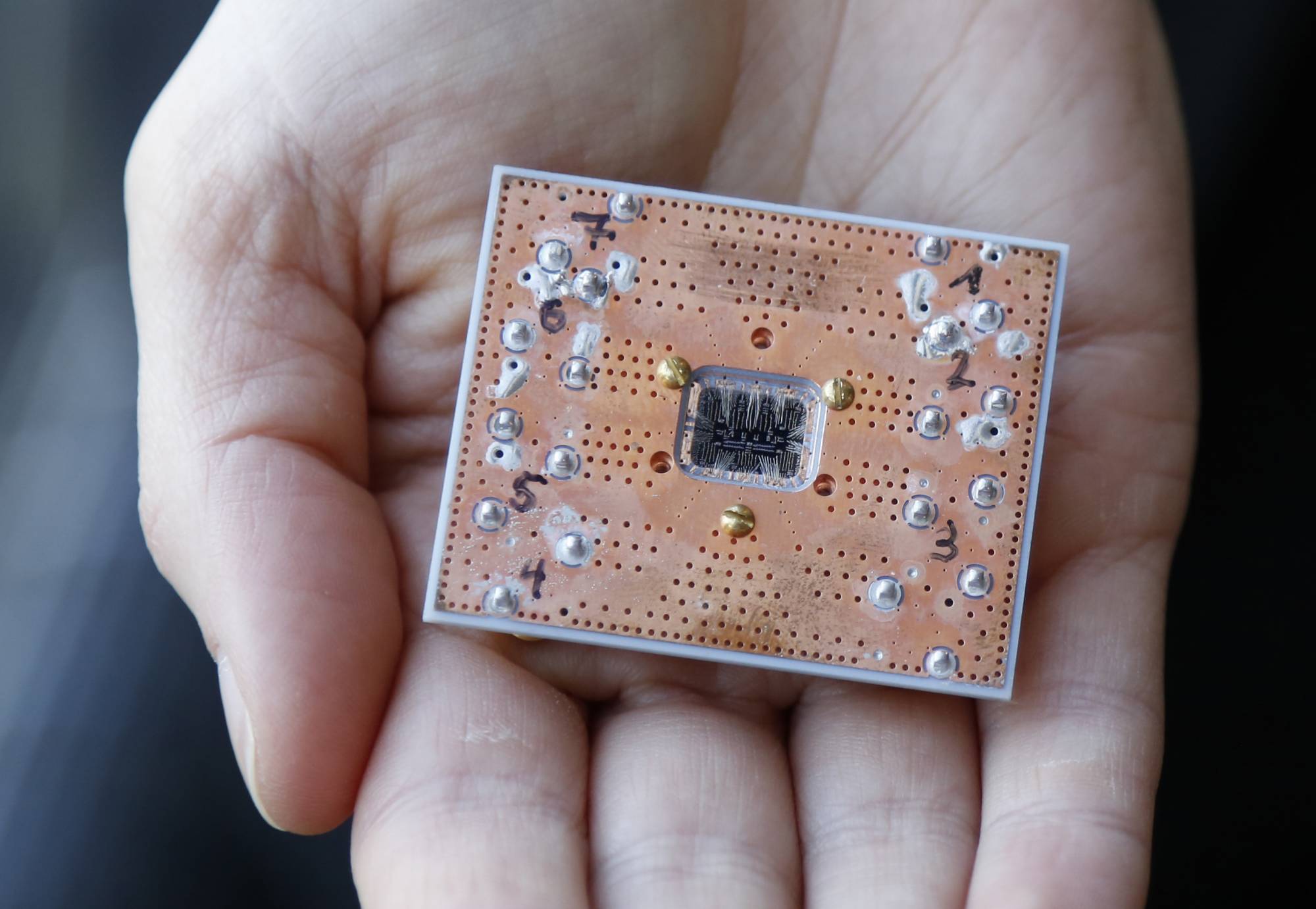
Can the government prevent a grid shutdown from a quantum cyber attack?
What the federal government can do to protect against the threat of quantum computing
Best listening experience is on Chrome, Firefox or Safari. Subscribe to Federal Drive’s daily audio interviews on Apple Podcasts or PodcastOne.
If wind and solar don’t wreck the energy grid, emerging quantum computing sure could. Brownouts here and there could turn into a sudden national catastrophe. For how the federal government can help prevent this, the Federal Drive with Tom Temin turned to the head of cybersecurity at Quantinuum, Duncan Jones.
Interview transcript:
Tom Temin: The grid is of concern to the Cybersecurity and Infrastructure Security Agency (CISA) and quantum. Those two things coming together seemed to scare them. And I guess it should scare all of us. What is the issue with quantum in particular, and the grid in particular, and what is CISA advising these days?
Duncan Jones: So if we talk briefly about quantum generally, the threat that we face from emerging quantum computers is that they will break many of the encryption schemes that we rely upon today. And we’ve seen a flurry of announcements and guidance out of the U.S. administration is really encouraging agencies to start taking this threat seriously, and to begin preparing to migrate to newer cybersecurity approaches that will be resilient to this threat. Now, the reason why it’s particularly relevant to critical national infrastructure is because in these sorts of environments, if you imagine, here, we’re talking about power grids, we’re talking about systems that could be 30, 40 years old, that are getting connected up to the internet, as part of this sweeping digitalization that we’re seeing in many industries. These systems are deployed in the field for decades. The return on investment makes sense if they’re there for 20 or 30 years. And therefore, these systems need to be built on a cryptographic foundation that can stand the test of time. And during that timeframe of 20, 30 years, we’re going to see quantum computers emerging that can break the encryption that we use today. So it’s particularly important in this sector, that these migrations are planned and are carried out effectively. Otherwise, you know, the nation is at risk.
Tom Temin: Now I have two questions, one, the operating systems and the applications used in critical infrastructure. And you see this all the time. Sometimes the grid operators have rather old applications and infrastructure to run it on. You see this when subways flood and they find relays that were put there in 1964, and this kind of thing. Are those applications and the data associated with them even encryptable by modern algorithms?
Duncan Jones: Yeah, the good news is yes. So you know, there is a process going underway at the moment in various industrial settings to bring these systems online. And it has to be done carefully. And what it typically relies upon is that you have this is where edge computing as a concept comes in, because you need to connect these, like you say steam powered sometimes systems to the internet. So what you tend to do is you drop something into a plant that is a relatively modern piece of kit. And it then talks to all of these systems and kind of mediates between that place and the rest of the world. And so what we’re talking about here, when it comes to the quantum threat is can we make sure those sorts of control systems as they’re being introduced, are future-proofed? So they’re ready to address the threats that we know about today. But also these ones that are coming down the line, including quantum.
Tom Temin: Right. So in that architecture, the encryption lies between the internet and the ancient operating system and applications, in other words.
Duncan Jones: Yes, I mean, it varies, of course. And obviously, new systems are being deployed all the time. We’re seeing, you know, a wonderful increase in solar and wind energy. And these systems are being developed and deployed today. And in those systems, it’s far more sophisticated. You’ll see those devices themselves connecting to the cloud and sharing information about what they’re doing. And but even there, we need to see that those security choices being made are future-proofed. So we need to be both ready for the quantum threat and also potentially embracing quantum as a tool to help us keep those systems secure.
Tom Temin: Sure, and not to get too deep into the weeds. But again, getting back to the older systems, is there any plan? Or do you see the practice of people, rather than running the old software, somehow abstracting it and running it in an emulation system, which could then change the architecture and change where you need to apply your encryption?
Duncan Jones: Yeah, so in this industry, there is this practice known as digital twins, where what you often try and do is in the cloud, you want like a shadow image of what’s on the on the plant floor. So you want to have this model of your steam powered, you know, generator turbine thing represented digitally, so you know what’s happening and if you make a change to the digital version of it, it gets reflected in the real life. What that boils down to is that you need a connection that you can trust between the clouds, let’s say, and some industrial plant buried somewhere in a inaccessible location. And that all sits on top of encryption and trusting that we’ve seen recently in the world, when global powers, come together and joust over territory. Cyber attacks are real, and the ability to disrupt power grids and things that really bring a country to its knees, they’re going to happen in the future. So this is why it’s so important and why I think CISA kind of specifically called out this area as somewhere that needs to focus on being quantum resilient.
Tom Temin: We’re speaking with Duncan Jones, head of cybersecurity at Quantinuum. And recently, NIST, the National Institute of Standards and Technology, issued a set of what it called quantum proof encryption algorithms, which they believe that even the future coming of quantum computers can’t crack. Does the solve the problem? Are we home free here, if everyone would simply adopt those algorithms?
Duncan Jones: It’s certainly a big part of the solution. Yes. These algorithms are based on mathematical problems that we don’t actually think quantum computers can solve any better than traditional computers. So this is why they represent a solution here. The challenge is that just kind of deploying these algorithms is something very difficult. So moving from what we have today, to effectively, you know, very different underpinnings. It’s a huge effort. And the starting point for many organizations is simply to understand what do they have today? You know, not all of their data is equally at risk from from the content threat. And so what many organizations will need to do and what CISA and recent security memos have stressed needs to be done. It’s a lot of planning, like, what do you have? Where are you using cryptography? Where does your data need to remain secure for like five or 10 years? You’ve got to understand that first to begin making the transition towards being quantum safe. And then these algorithms represent, I would say, one half of the challenge. The other half is, how do we make sure that we even have good encryption in the first place good encryption keys. And that’s one of the areas where actually we can start to use quantum as a as a positive force to help us develop encryption that is genuinely going to stand the test of time.
Tom Temin: What’s your sense of the state of quantum computing? Does anyone say Russia? Probably less Russia, the chance of them than China? But do they actually have a real quantum computer that they can throw at cyber hacking yet? Or is that 10 years off? Or maybe never?
Duncan Jones: Well, it’s interesting, you should mention China because Baidu recently announced their own superconducting quantum computer. So it’s clear that countries around the world are investing heavily in this technology. We don’t believe anybody today has a quantum computer that is actually powerful enough to start threatening encryption, that time will come and we may not know exactly when we’ve reached that moment. And perhaps more worryingly, there is this risk that the data that we’re exchanging today can be captured and recorded by these sorts of countries, we may not want to have access to it. And as their quantum computers develop and mature, they will be able to retrospectively decrypt it and have a look. So this is another one of the reasons why federal agencies need to take this seriously, because they are the sorts of organizations that share secrets, they share things that need to still be secret in 10 years time or 15 years time.
Tom Temin: Right, I get the sense that a good strategy then would be to learn how to deploy those quantum-proof algorithms. You said, that’s the most difficult task at this point. But you’re going to have to face that at some point. So why wait till the devil is knocking at the door? Maybe now’s the time to get familiar with them and get some body of knowledge on how to deploy them before you have to.
Duncan Jones: Yeah, absolutely. And this very much echoes the guidance that’s emerging. We have maybe 18 months or two years before this NIST process that you mentioned earlier, fully standardizes and announces this is exactly how we do these new algorithms. That is the window of time in which organizations public and private, need to get their plans in place and need to start doing testing and exploring, how can they be ready for the quantum threat? How can they use quantum as a tool? How do they just they just need to get their ducks in a row because we’re a couple of years away from being able to pull the trigger for this stuff into production, and people need to be ready.
Tom Temin: And maybe the second implication is that it’s a good time to review your basic systems architecture so that you can maybe simplify and apply the encryption in an efficient way, let’s say.
Duncan Jones: Yeah, very good point, Tom. Yeah, so there’s a buzzword in the industry, the cyber industry of crypto-agility, which describes if a system is crypto-agile, it means that it’s not a big deal if you change algorithms from time to time. Many of our systems today are not crypto-agile. And so this transition period is going to be painful. But if we approach it in the right way, as you as you suggest, we could make sure that future transitions are far easier. So yes, a very good point.
Tom Temin: And a final nerd question, are we making progress in the concept of encryption, while data is in use by the processor?
Duncan Jones: it’s an active area of research, it used to be something that was very, very slow, and therefore it wasn’t particularly appealing to people. But there have been advances recently that mean, it’s starting to become more feasible to operate on data that is completely encrypted, it means you never have to decrypt it in the first place. I expect we’ll see more of that emerging in the future.
Tom Temin: So someday, we’ll be able to send those quantum computers into endless loops.
Duncan Jones: Well, yeah, I mean, endless loops, entanglement superposition, anything’s possible with a quantum computer.
Tom Temin: All right. Duncan Jones is head of cybersecurity at Quantinuum.
Copyright © 2024 Federal News Network. All rights reserved. This website is not intended for users located within the European Economic Area.
Tom Temin is host of the Federal Drive and has been providing insight on federal technology and management issues for more than 30 years.
Follow @tteminWFED
Related Stories