DoD to release, start implementing new zero trust strategy by Oct. 1
The strategy will encompass ways to implement zero trust on legacy networks, commercial clouds, and private clouds. Officials say they are already in talks with...
Best listening experience is on Chrome, Firefox or Safari. Subscribe to Federal Drive’s daily audio interviews on Apple Podcasts or PodcastOne.
The Defense Department is ready to get serious about transitioning its network defenses to zero trust principles. The Pentagon expects to release a formal zero trust strategy by mid-September, wants to have an enterprise-wide zero trust implementation in place by 2027, and is already in talks with commercial providers about how to implement zero trust in the cloud.
Last year’s White House executive order on cybersecurity told all federal agencies to draw up plans to move to a zero trust architecture. DoD published its first reference architecture shortly before the EO, and has since updated it to a 2.0 version. But Defense officials said the strategy set to be released next month will lay out the specific steps DoD components and their vendors will need to take to implement zero trust.
“We are committed to implementing zero trust at scale for our 4 million-person-plus enterprise that we lead,” John Sherman, DoD’s CIO said during a speech at a Fedscoop event this week. “We’re not reinventing the wheel, not trying to do something that’s already been tried successfully in one of the services, but building on all that. What we’re aiming for by 2027 is to have zero trust deployed across a majority of our enterprise systems. That’s an ambitious goal, but the adversary capability we’re facing leaves us no choice but to move at that pace.”
DoD’s definition of zero trust includes 45 separate “capabilities” organized around seven “pillars”: users, devices, networks and environments, applications and workloads, data, visibility and analytics, and automation and orchestration.
From there, the strategy will map out 90 separate “activities” that need to be accomplished. Some are technology-related, but many are not, said Randy Resnick, the director of DoD’s zero trust portfolio management office.
“We’re describing a cybersecurity IT solution, but there’s also other things that need to be changed when you move to zero trust,” he told a conference hosted by the Digital Government Institute this week. “You have policy that might be needed to be upgraded. You might need to hire different sorts of people. You have to have leadership informed of this and fully backing the transition. You have training that’s going to be required. So all these other things are non-IT, but equally important as you move to zero trust, because it is a radical change.”
Resnick said the strategy will also lay out three separate courses of action for zero trust: one for applying the principles to DoD’s existing IT infrastructure, a second for implementing zero trust in commercial cloud environments, and a third for government-operated private clouds.
The department has already had early discussions with commercial cloud providers to gauge how well DoD’s zero trust definitions could map on to their computing environments.
“We’ve shared with them our definition of zero trust and what they would need to do in the cloud. We asked them, ‘Can we implement zero trust in your current cloud?’ And they came back to us with numbers that seemed to indicate the answer was yes,” Resnick said. “So the next step is to independently evaluate their assertions, and we believe we’re going to get that body of evidence in maybe two or three weeks. That’s going to be evaluated, likely by [the National Security Agency]. And then we’re going to pivot to a pilot, because nobody’s going to want just a guess.”
Resnick said the pilot isn’t officially planned yet, but officials are considering one that would use cloud environments the Army and Air Force already have running under their own contracts with commercial providers.
“We would roll in the zero trust overlay for that particular cloud solution, and then we would document it heavily: How does it work? How do you configure it? Are their easier ways to do it? And then we would run apps and data through it, and ultimately run a red team against it to see whether or not that overlay would be effective against the adversary,” he said. “Nothing is going to be rolled out in the DoD unless we know it’s rock solid, so we will be doing multiple pilots in fiscal ’23 to do that.”
Those pilot projects will be one of the first zero trust priorities when the new fiscal year starts on October 1. So far, the department has conducted one small pilot using its own IT infrastructure, but otherwise the architecture and activities it’s defined haven’t been tested in a real-world environment.
Another key question is what the IT industry, beyond the cloud providers, will need to do to support DoD’s strategy. One thing that’s already clear though, Resnick said, is that the department’s needs can’t be filled by any single company.
“No vendor can achieve all 90 of the activities within their own product line, so vendors are going to have to team and integrate together in order to create a solution set for the Department of Defense,” he said. “I’m making up a number, but it might be eight or 10 vendors, perhaps, that have to all work together to generate an outcome such that they get close or they hit the 90 activities. But it’s not up to the DoD CIO to say they hit it. The Risk Management Framework is still in place. You have the concept of authorizing officials, which are still in place, and they’re going to have to accept the risk based on the controls and the evidence provided to them to grant an authority to operate.”
But there’s likely to be plenty of money in the DoD budget to support the effort.
Resnick said department leaders have long recognized that the move to zero trust would require billions of dollars in up-front spending. And although Congress hasn’t yet approved the DoD budget for next year, there’s money set aside in the department’s budget request.
“There’s a myriad of reasons why we have technical debt and we have not invested in in our own networks over the last 10 years, which would indicate that we’re way behind the eight ball. But people understand that if we want to really have a leap ahead, and to fully change our networks in a way that would actually stop an adversary, it’s going to take the whole of the DoD, if not whole of government to make happen,” he said. “We don’t know how much money it’s going to take, but we’re getting close. Because as the services get their hands on this and they start implementing, they’ll better understand what their gaps are, what it takes to fill those gaps, and what vendors or capability there is to do that, and more accurate dollar figures will come about. So it’s very complex, but added dollars are being implemented to help facilitate the acceleration of zero trust adoption.”
Copyright © 2024 Federal News Network. All rights reserved. This website is not intended for users located within the European Economic Area.
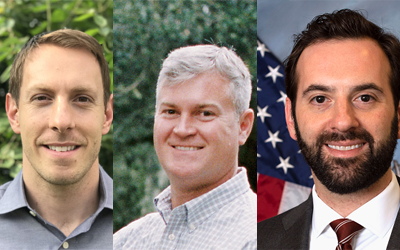
Jared Serbu is deputy editor of Federal News Network and reports on the Defense Department’s contracting, legislative, workforce and IT issues.
Follow @jserbuWFED