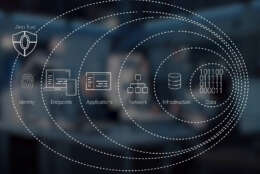
zero trust
-
The Army is in the midst of collapsing all of its networks, aiming to achieve a "unified network" within the next three years.
January 12, 2024 -
While the buzzword of 2024 may be artificial intelligence, or some derivative like generative AI or large language models, the biggest challenge and focus for federal IT community will continue to be the people.
January 09, 2024 -
The Energy Department created standard training courses to ensure employees have a baseline understanding of zero trust requirements, while the CFBP is focused on software development, including open source software.
December 29, 2023 -
U.S. Indo-Pacific Command says it's starting with a clean sheet of paper on the topic of network defense, building a mission partner network that incorporates zero trust from the beginning.
December 28, 2023 -
This year Federal News Network heard from top defense tech officials about their priorities, developments and plans as the DoD is moving forward with its modernization efforts in line with the National Defense Strategy.
December 27, 2023 -
Wayne LeRiche, the federal civilian field chief technology officer and solutions architect for Palo Alto Networks Federal, said secure access service edge (SASE) sets a framework for agencies to get more easily implement a zero trust architecture.
December 20, 2023 -
Zero trust is driving the security conversation today across both the public and private sectors. Within government, it’s a top priority as evidenced by the directives, mandates and policies that have been issued by the…
December 15, 2023 -
Herb Kelsey, the Project Fort Zero Team Leader at Dell Technologies, said agencies have the opportunity to focus on the policy and process side and not the technology piece of the zero trust architecture.
December 04, 2023 -
As zero trust increasingly becomes the norm, especially in fed, not only can we expect to see more resilience, but a greater ROI in cybersecurity overall. We just have to continue to make progress on our zero trust plans with speed and transparency at the forefront of our collective approach.
November 10, 2023 -
Randy Resnick is the director of Zero Trust Architecture Program Management Office in the DoD’s CIO’s office. A team of 17 to 18 people will analyze the zero trust plans submitted by 43 services and agencies.
October 24, 2023 -
Traditional security controls are insufficient in protecting against major security breaches. They tend to be reactive, static, noncontextualized around threats and are often based on compliance requirements and information technology practices. As a result, traditional security controls are not responsive enough to anticipate, evolve and adapt to threat actors’ behaviors and activities.
October 19, 2023 -
In the realm of federal cybersecurity, change is both inevitable and necessary. The urgency of President Biden's 2021 Executive Order to implement a zero trust architecture by September 2024 has set the stage for a pivotal transformation. Yet, as the deadline draws near, it's apparent that while the directive's intent is clear, the path to its realization is fraught with complexity and challenges.
October 12, 2023 -
As the government continues to modernize, zero trust remains a top priority. Agencies can leverage this potential influx of funding to make strategic investments that achieve zero trust goals.
September 29, 2023 -
Zero-trust architecture has been top-of-mind for the federal government, especially as we approach the one-year countdown for the White House’s zero-trust memorandum deadline.
September 12, 2023 -
Lt. Gen. Robert Skinner, DISA’s director and commander of the Joint Force Headquarters-Department of Defense Information Network (JTF-DoDIN), said the agency is undertaking three separate tests of tools to better protect internet boundaries.
September 08, 2023