Best listening experience is on Chrome, Firefox or Safari. Subscribe to Federal Drive’s daily audio interviews on Apple Podcasts or PodcastOne.
Industry groups are pressing the Biden administration for more time before it potentially rolls out new rules requiring federal contractors to provide purchasing agencies with a “software bill of materials.”
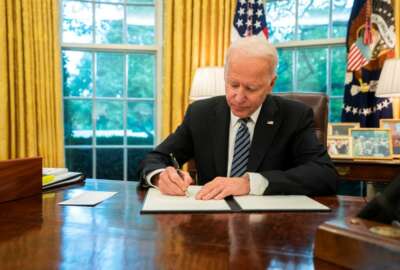
The “SBOM” is one of the cybersecurity practices the government is considering as it shapes new requirements under President Joe Biden’s May executive order. The order requires the National Telecommunications and Information Administration to publish by July 11 the “minimum elements” for an SBOM.
Allan Friedman, director of cybersecurity initiatives at NTIA, said his agency is on track to meet the deadline.
“We are going to be having a public document that defines the minimum elements of SBOM and sort of lays out as well a path to the future of how do we go from minimum elements to sort of expanding it,” Friedman said during a June 21 event hosted by the R Street Institute. “And then other parts of the government will be up picking that up and working with NTIA to think about what that looks like from a federal procurement rules perspective. And NTIA will continue to shepherd the stakeholder community to focus on implementation at scale.”
The executive order defines an SBOM as ‘‘a formal record containing the details and supply chain relationships of various components used in building software.’’
Friedman said one of the “slightly imperfect analogies” is the ingredients listed on the back of food packaging.
“[Software] is assembled out of different pieces in different layers, often open source,” he said. “And many of these components are out of date, like ingredients lists, they could be rotten or stale, or, in the case of cybersecurity, actively compromised. And so software bills of material or SBOMs are the first step towards having greater transparency into our supply chain.”
Since 2018, Friedman has led NTIA’s work on a software transparency initiative aimed at defining SBOMs in partnership with other industry, academia and government stakeholders. The work has led to several proof-of-concepts in the healthcare, energy and automotive sectors.
“It won’t solve everything,” Friedman said. “There are lots of other ways that someone might want to attack the supply chain, going after the tools themselves, for example, but at the very least we can say what the components are.”
In a request for comments released in June, NTIA previewed the minimum elements document, including proposed data fields, operational considerations and support for automation. More than 80 organizations responded to NTIA, including a range of companies and industry groups, with many offering technical feedback and considerations.
But groups also suggested any rush to implement new SBOM requirements on contractors would be ill advised.
“The Chamber shares many of the administration’s goals regarding an SBOM,” the U.S. Chamber of Commerce wrote in a June 17 letter to NTIA. “Nonetheless, the EO’s complexity and aggressive timelines may hamper the methodical consensus building that is still needed to develop an SBOM, particularly for federal contracting, that achieves mutual industry-government goals, such as increased software transparency, trust, innovation, and security.”
The National Defense Industrial Association also urged caution in developing SBOM requirements.
“We hope that our comments and questions will help NTIA create and publish a list of ‘minimum elements for an SBOM’ that raises the bar on security while also giving due consideration to costs and benefits of new requirements,” NDIA wrote in a letter to the Commerce agency. “Indeed, a rushed rollout of new rules could ultimately lead to setbacks in our shared goal of improving cybersecurity defense in the United States as we have seen in other areas.”
But Friedman noted the cybersecurity executive order’s deadlines may not give industry as much time as they would like.
“One of the challenges that we sometimes see is the community playing for time and saying, ‘Well, let’s spend our time arguing over some of the minutiae here and here,’” he said. “And I think just looking at the timelines that have been laid out in the EO, I think there’s going to be less tolerance for that today. And so, as the community starts to say, ‘how are we going to mobilize and respond,’ I think that strategy will probably not be as effective.”
The administration also has some key supporters for its initiatives in Congress. Rep. Jim Langevin (D-R.I.), chairman of the Armed Services cybersecurity subcommittee and a member of the Cyber Solarium Commission, also filed comments with NTIA on the SBOM proposal.
“I write to strongly encourage NTIA to use the findings of its multi-stakeholder process around software component transparency to publish the minimum elements of a SBOM as quickly as possible,” Langevin wrote.
Langevin also urged the agency “to avoid projecting how its standards may affect federal contracting.” The executive order directs the National Institutes for Standards and Technology to come up with software security standards for federal agencies, while also directing the Office of Management and Budget to enforce NIST’s work through requirements.
“NTIA should not attempt to guess how SBOM requirements might affect future contract negotiations carried out by the General Services Administration and other departments and agencies,” Langevin wrote. “The Federal Government’s purchasing power is immense, and NTIA should not limit the ability of procurement officers to strike the best possible deal for federal customers.”
Copyright
© 2024 Federal News Network. All rights reserved. This website is not intended for users located within the European Economic Area.